Interactive demo
Simulate the full flow - no data is sent to the server
The complete flow
From the DAPI certificate to publication in the EVIDE public registry. Click on each phase to learn more.
Verifiable evidence chain
Each intake remains independent and immutable, but can be linked to the previous one to verifiably document the evolution of content, decisions and versions over time.
One verified identity, multiple organisations
A single DAPI identifies the person. The same verified identity can operate across multiple distinct organisational perimeters, keeping requests, chains and billing separate.
Try the simulation
Choose the evidence type, upload a file or enter text, and see the system in action. All in your browser.
Verified DAPI identity
In the real system, you log in with your 10-digit DAPI code. Your identity is verified by Informatica in Azienda before you receive the certificate.
In the real system this number is unique and certified.Forensic Cross-Check
The evidentiary quality indicator computed by EVIDE at intake time.
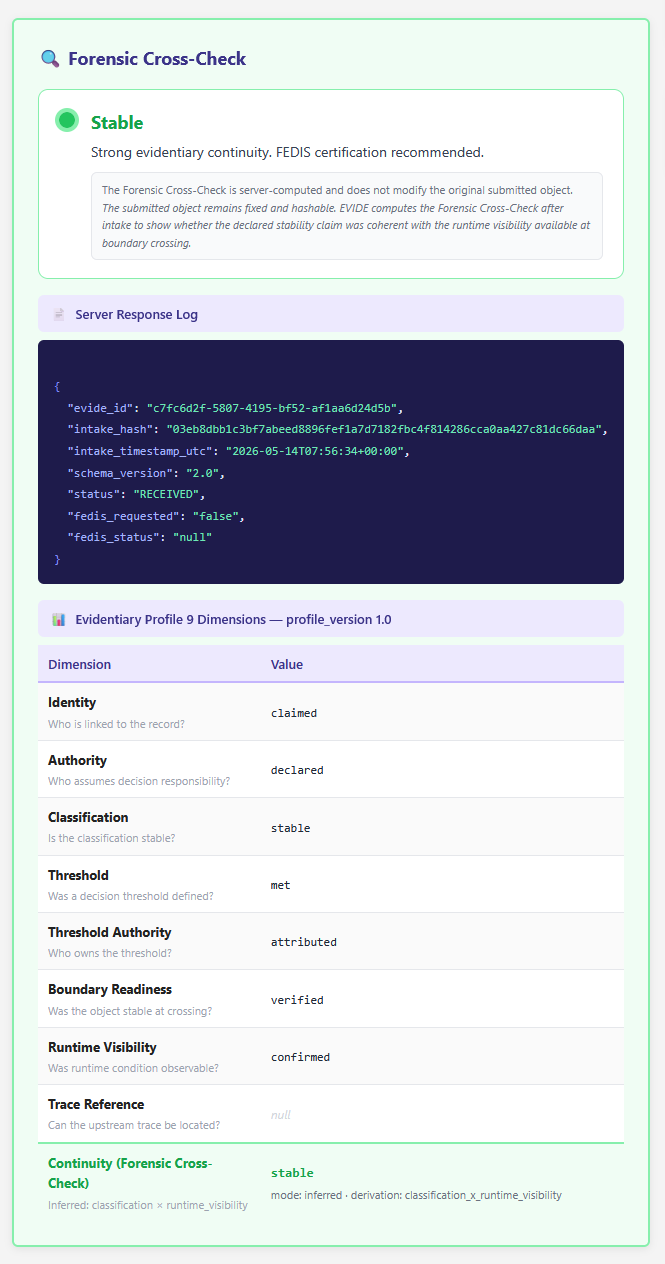
Stable
Strong evidentiary continuity. FEDIS certification recommended.
classification = stable × runtime_visibility = confirmed
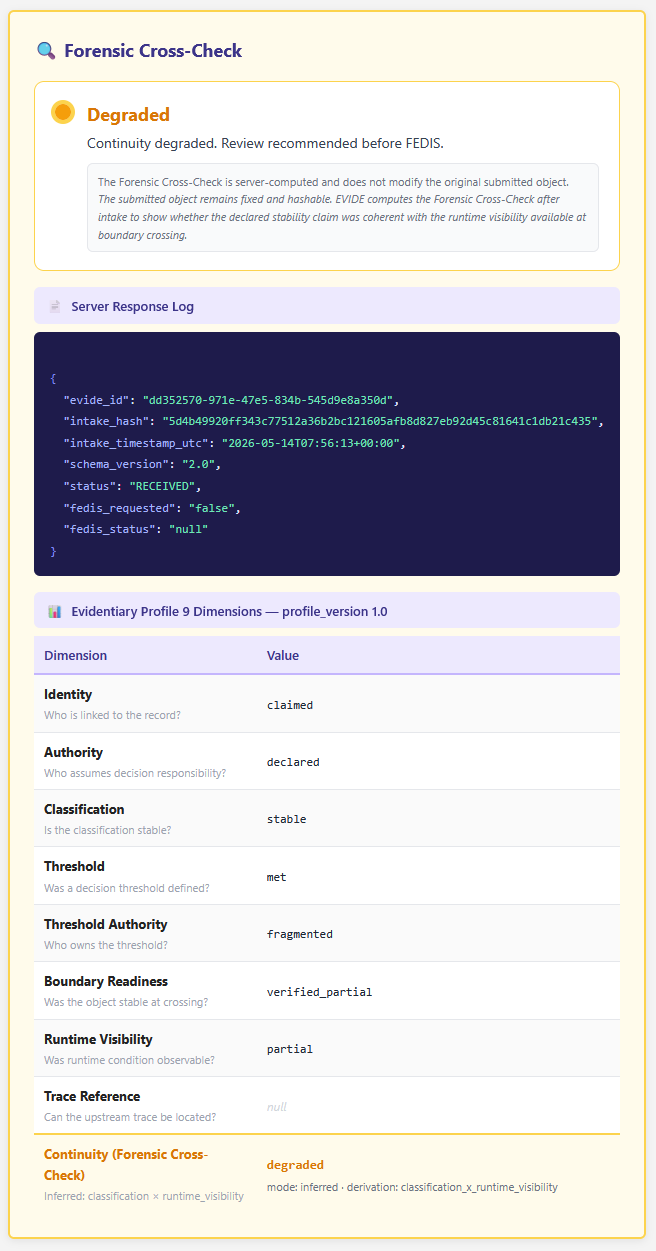
Degraded
Continuity degraded. Review recommended before FEDIS.
classification = stable × runtime_visibility = partial
— or —
classification = provisional × runtime_visibility = confirmed/partial
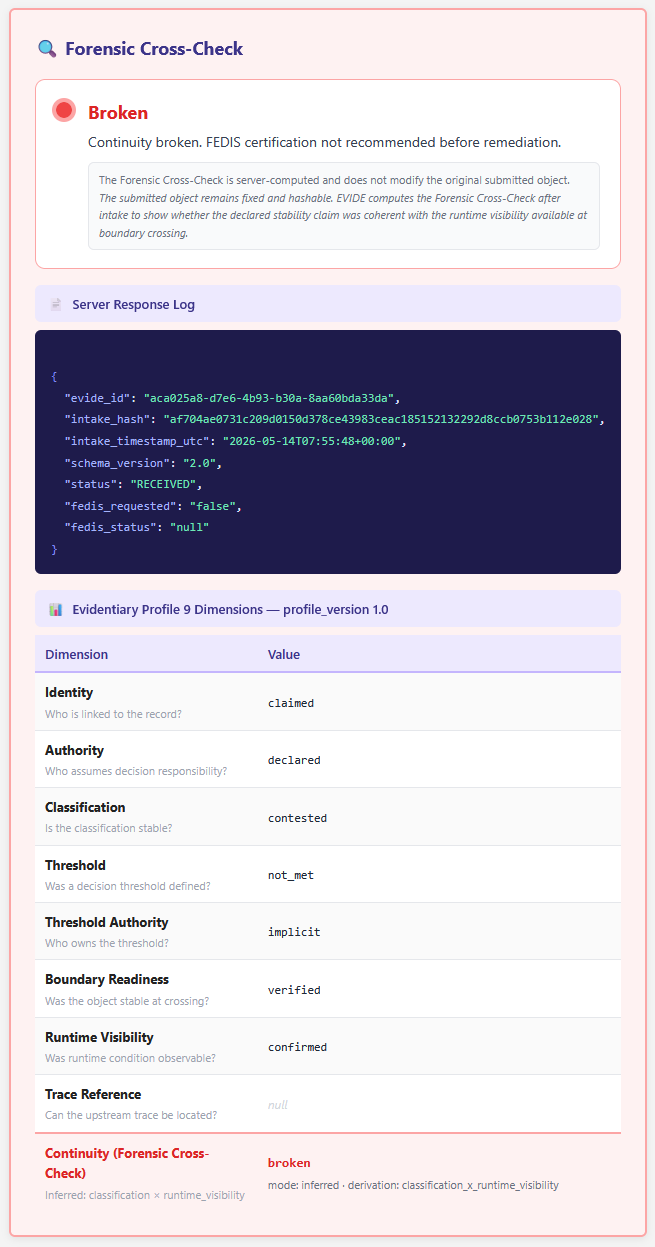
Broken
Continuity broken. FEDIS certification not recommended before remediation.
classification = contested × any runtime_visibility → always broken
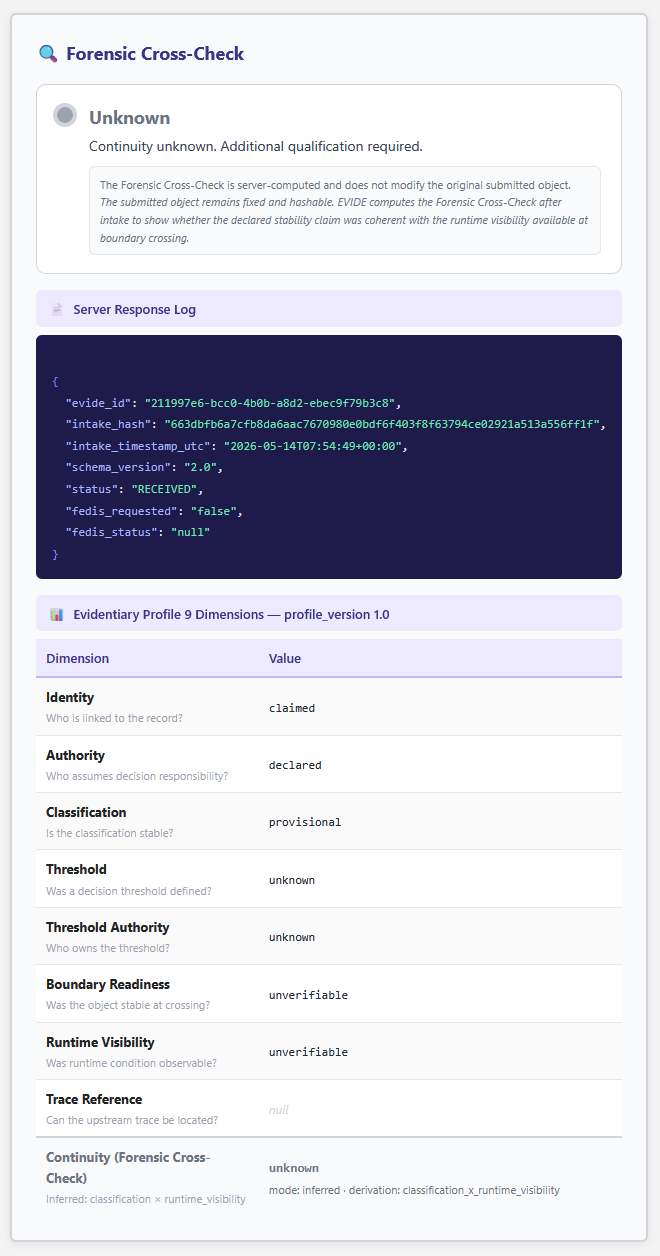
Unknown
Continuity unknown. Additional qualification required.
classification = null or runtime_visibility = null
— or —
classification = provisional × runtime_visibility = unverifiable